At 2:21 AM UTC on a quiet Sunday morning, someone turned $100,000 in USDC into roughly $25 million in extracted value. The weapon was a broken minting function on Resolv Labs’ USR stablecoin. The damage spread across lending vaults, DEX liquidity pools, and the confidence of anyone betting on newer stablecoin designs.
Here’s what happened, how it happened, who got hurt, and what it actually means.
What Is Resolv, and Why Did It Matter?
Resolv is a stablecoin protocol built around a delta-neutral strategy. USR, its dollar-pegged token, was collateralized by a mix of ETH, staked ETH, and Bitcoin, with perpetual futures hedging out directional price risk. The protocol also had a second token, RLP (Resolv Liquidity Pool), which acted as a junior tranche, absorbing losses before USR holders would take any hit. Think of RLP as the shock absorber, USR as the supposedly safe seat.
At peak, Resolv held over $500 million in TVL. It had raised $10 million in seed funding from names like Coinbase Ventures, Maven 11, and Animoca Brands. It was integrated into Morpho, Aave, Euler, Curve, and a string of other DeFi protocols. It was audited. It had partnered with Hypernative for real-time threat monitoring. On paper, the setup looked solid.
But TVL had been bleeding badly before the exploit even happened. USR’s market capitalization dropped from approximately $400 million in early February to around $100 million just weeks before March 22. That is a 75% contraction. Whether that was insiders quietly unwinding, yield farmers chasing the next opportunity, or something else entirely, nobody has answered yet. The timing is uncomfortable.
The Exploit: A 500x Over-Mint
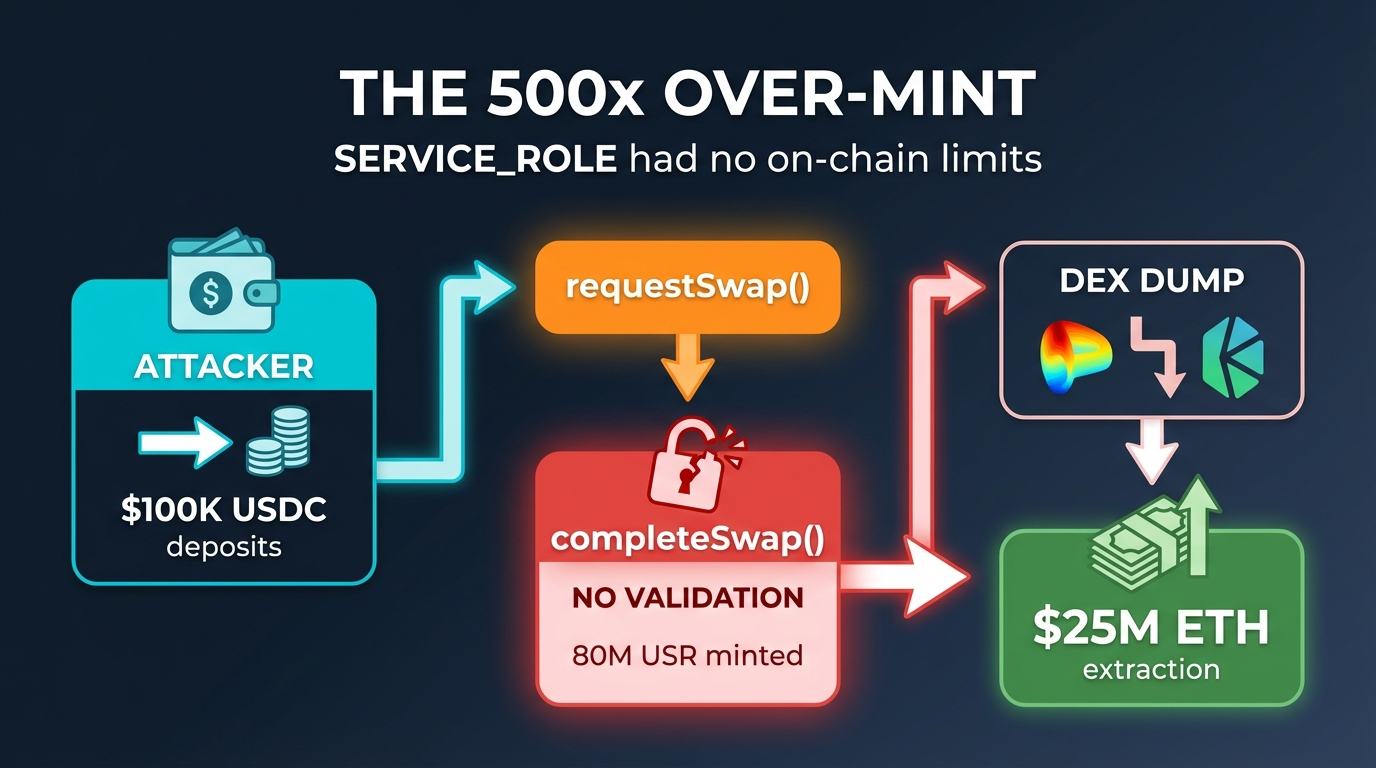
The attack targeted Resolv’s two-step minting flow: requestSwap() followed by completeSwap().
In normal operation, a user would deposit USDC via requestSwap(), creating a pending request. Then a privileged off-chain signer (the SERVICE_ROLE) would call completeSwap() to finalize the mint, issuing USR proportional to the deposit. One dollar in, one USR out.
The problem: there were no on-chain guardrails enforcing that ratio. The SERVICE_ROLE could pass any mint amount it wanted to completeSwap(), and the contract would just execute it. No maximum mint limits. No price-oracle checks. No bounds validation between the request and the completion. As on-chain researcher @andrewhong5297 pointed out, the service role was a plain externally owned address (EOA), not a multisig. The admin role was a multisig, but the service role, the one with the power to mint arbitrary amounts, was not.
The attacker deposited roughly $100,000 to $200,000 in USDC across a few requestSwap() calls. Through the broken completeSwap() flow, approximately 80 million USR got minted, about 50 million in one transaction and another 30 million shortly after. That is a 400x to 500x over-mint.
D2 Finance, the crypto research fund that published one of the first analyses, put it bluntly: either the oracle was gamed, the off-chain signer was compromised, or the amount validation between request and completion is simply missing. Security analysts at Cyvers and analysts like @andrewhong5297 leaned heavily toward the third explanation, combined with a likely compromised private key. This wasn’t a reentrancy attack or a flash loan exploit. It was a privileged role with too much power and too few checks.
The Cashout: 17 Minutes to the Bottom
Once the 80 million USR were minted, the attacker moved fast. D2 Finance described it as a textbook DeFi hack cashout running at full speed.
The newly minted tokens were dumped across decentralized exchanges, including Curve, KyberSwap, and Velodrome. USR was swapped for USDC, USDT, and then aggressively converted into ETH. PeckShield tracked over $4.55 million worth of ETH (roughly 9,100 ETH) converted in early transactions alone. The total extracted value landed somewhere around $23 to $25 million, limited mainly by available DEX liquidity and slippage.
USR’s price collapsed. On Curve’s USR/USDC pool, it hit a low of 2.5 cents, just 17 minutes after the first 50 million mint. On CoinGecko, the reported low was around $0.20 to $0.257, a 74% to 97% crash depending on the venue. It later recovered partially, floating around $0.80 to $0.87 on some pairs, but at the time of writing the depeg persists significantly, with some trackers showing USR as low as $0.05 to $0.07.
Multiple failed transactions were visible on-chain during the dump, showing the attacker racing to exit before liquidity dried up entirely.
Resolv’s Response
Resolv Labs confirmed the exploit on X, stating they had paused all protocol functions and were investigating. Their statement emphasized that the collateral pool remains fully intact and no underlying assets were lost, framing the issue as isolated to USR issuance mechanics.
That framing is technically accurate but also somewhat disconnected from what happened to users. The collateral backing pre-exploit USR still exists. But anyone holding USR bought on the open market, or anyone who minted USR legitimately and didn’t exit before the crash, is sitting on tokens worth a fraction of a dollar. Recovery via pre-exploit snapshots is the expected path forward, but no concrete plan has been announced.
The Contagion: Who Got Caught in the Blast
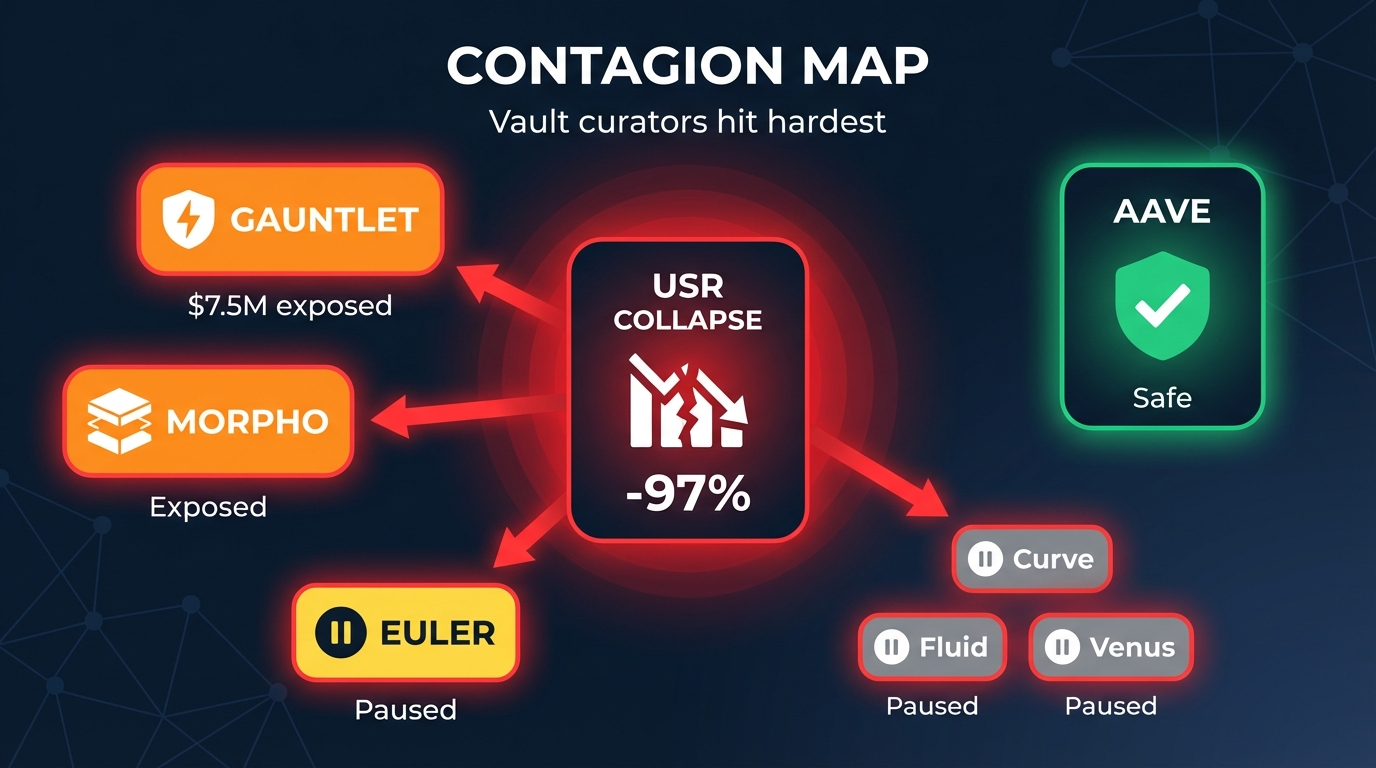
The damage didn’t stay contained to Resolv. USR and its wrapped/staked derivatives (wstUSR, RLP) were integrated into lending markets and curated yield vaults across DeFi. When USR’s price collapsed, the contagion spread through those integrations.
Gauntlet, one of the largest vault curators on Morpho, was the most visibly affected. Their initial statement acknowledged the exploit quickly and described most vaults as unaffected, with only a few high-yield vaults carrying limited exposure. But community analysis told a more specific story. Gauntlet USDC Core on Ethereum had a reported allocation of around $4.95 million to a wstUSR/USDC market, with high utilization and low available liquidity after the depeg. Gauntlet USDC Frontier and a dedicated Resolv USDC vault were also exposed. On-chain observers estimated total direct exposure across affected Gauntlet vaults at over $7.5 million. Gauntlet paused deposits on certain Morpho Frontier and Core vaults to manage liquidity.
Steakhouse Financial, another major Morpho curator, had dedicated Resolv USR vaults and served as a risk manager and consultant for Resolv itself. Ironically, Steakhouse had published a detailed risk assessment of the Resolv protocol just days before the exploit, which actually discussed exploit scenarios as a theoretical risk. They have confirmed no direct exposure in their main vaults.
Euler Labs announced it was investigating the unauthorized minting incident and had taken measures to isolate risk.
Aave came out clean. Stani Kulechov, Aave’s founder, confirmed zero risk exposure to USR. Resolv had participated in Aave as a liquidity provider, but its collateral assets were already deposited and remain unaffected. Resolv is reportedly repaying its debt and exiting Aave in an orderly fashion.
Other protocols, including Fluid/Instadapp, Venus, Inverse Finance, and Lista DAO, paused USR-related markets as a precaution. Some, like the kpk (karpatkey) team, acknowledged limited RLP exposure in certain yield vaults but had positions closed or withdrawn.
The Uncomfortable Questions
Why was a single EOA controlling mint authorization? The admin role used a multisig, but the SERVICE_ROLE, the role that could literally print money, was a regular wallet address. This is an extraordinary amount of trust placed in a single key. Even if it was a compromise rather than an inside job, the architecture made it trivially exploitable once that key was obtained.
Why were there no on-chain limits? No maximum mint per transaction. No per-epoch caps. No sanity check comparing the deposit amount against the minted output. These are basic protective measures. Their absence is hard to explain for a protocol managing hundreds of millions in TVL.
What happened to the audits? Resolv’s contracts were audited. They had partnered with Hypernative for monitoring. They ran an Immunefi bug bounty, including a contest where researchers competed to find vulnerabilities. And yet the core minting flow, the single most sensitive function in a stablecoin protocol, shipped without proper validation. As Cyvers put it in their post-exploit analysis, the contracts were audited but the issue still allowed unauthorized minting without proper validation.
What explains the pre-exploit capital flight? A 75% drop in market cap over roughly six weeks, from $400 million to $100 million, is not normal organic behavior. It could be unrelated to the exploit. Yield farming capital is notoriously fickle, and Resolv’s points program had ended, which often triggers exits. But the scale and timing invite scrutiny.
Broader Lessons
This exploit is not a novel attack vector. It is closer to a failure of basic operational security. The minting flow relied on trust in an off-chain signer with no on-chain enforcement of correct behavior. That is a design choice, not a bug in the traditional sense. The contract did exactly what it was told to do; it’s just that nobody should have been able to tell it to do that.
For anyone participating in DeFi yield strategies, the Resolv incident is a reminder that integration risk is real and compounding. A yield vault curator allocating to a Morpho market that lends against wstUSR is three layers removed from the underlying minting contract. Each layer adds convenience and yield. Each layer also adds exposure to failures you may not have the tools or time to evaluate.
Resolv’s TVL trajectory also illustrates the gap between growth and maturity. The protocol went from under $50 million to over $650 million in under three months during its first points season, driven largely by leverage looping on Morpho and Euler. Growth like that attracts capital, integrations, and attention. But it also means the protocol was load-bearing for hundreds of millions of dollars while still running a mint flow controlled by a single wallet.
What Happens Next
Resolv has paused all protocol functions. Recovery for legitimate holders via pre-exploit snapshots looks likely, based on precedent from similar mint exploits where inflated supply can be rolled back while underlying collateral remains. But no timeline or specific mechanism has been published.
The attacker’s wallet is being tracked by PeckShield, Cyvers, D2 Finance, and community researchers. A significant portion of the extracted value has already been converted to ETH.
For users in any Gauntlet-curated vaults, particularly USDC Core and Frontier, it is worth checking positions directly on Morpho. Liquidity constraints may temporarily affect withdrawals on markets with USR/wstUSR/RLP exposure.
No full postmortem from Resolv Labs has been released. When it comes, the key questions will be: how was the SERVICE_ROLE key secured, what monitoring was in place for anomalous mints, and why the validation gap existed in a function that had been part of the contract since deployment.
Until then, the protocol sits frozen, and DeFi has another case study in why the boring parts of security, key management, access controls, input validation, matter more than the clever parts.
